Modern cybersecurity professionals no longer view endpoint protection as a secondary defensive layer but rather as the primary battleground where the integrity of an entire corporate network is decided. Microsoft Defender for Endpoint represents a fundamental shift in how organizations approach this challenge, moving away from the antiquated model of signature-based scanning toward a holistic, cloud-delivered ecosystem. This platform is defined not merely as a security tool but as a sophisticated integration of behavioral analysis, machine learning, and massive-scale threat intelligence that empowers businesses to prevent, detect, and respond to advanced persistent threats. The primary objective of choosing the right license is to align an organization’s specific risk profile and technical maturity with the appropriate level of protection, ensuring that the defensive posture is neither overkill for a small firm nor dangerously insufficient for a global enterprise. By leveraging the trillions of signals processed by the Microsoft security graph, the platform provides a level of visibility that was previously reserved for only the most elite security operations centers.
Advanced Defensive Pillars and Automation
The efficacy of a modern security strategy relies heavily on the strength of its foundational pillars, which prioritize proactive hardening over reactive cleanup. Attack Surface Reduction serves as the critical first line of defense by systematically shrinking the available entry points that a sophisticated hacker might exploit during the initial phases of an attack. This involves a rigorous process of hardening systems, such as disabling legacy protocols that are no longer necessary for business operations and blocking suspicious office macro behaviors that often serve as delivery vehicles for ransomware. By implementing these digital fortifications, IT teams can effectively neutralize entire classes of threats before they ever execute. Complementing this structural hardening is Next-Generation Protection, which replaces traditional, static antivirus engines with a dynamic system utilizing cloud-delivered machine learning. This capability allows the platform to identify and block zero-day threats in real-time, even when those threats have never been seen before in the wild, providing a safety net against the rapidly accelerating pace of malware development.
Moving deeper into the defensive stack, the transition from simple protection to comprehensive detection and response is where the true value of the ecosystem becomes apparent. Endpoint Detection and Response provides high-fidelity telemetry that essentially acts as a flight data recorder for every device on the network, capturing every process start, network connection, and file modification. This deep visibility is indispensable during an investigation, as it allows security analysts to reconstruct the timeline of a breach and understand exactly how an attacker moved through the environment. However, the sheer volume of data generated by these systems can lead to significant alert fatigue among IT staff. To combat this, Automated Investigation and Remediation uses AI-driven playbooks to examine alerts automatically, mimicking the steps a human analyst would take but at a much higher speed. The system can autonomously isolate a compromised machine from the network or terminate a malicious process, which significantly reduces the mean time to respond and prevents a localized incident from escalating into a full-scale corporate catastrophe.
Entry-Level and Enterprise Tier Comparisons
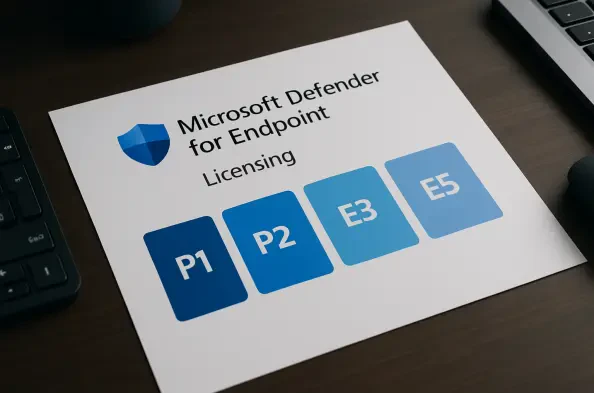
Navigating the various tiers of the Microsoft security stack requires a clear understanding of where the foundational features end and the advanced capabilities begin. Microsoft Defender for Endpoint Plan 1 is categorized as the entry point for organizations that need a solid baseline of protection but lack the staffing or requirement for deep, proactive threat hunting. This plan provides the essential components of next-generation protection and attack surface reduction rules, ensuring that devices are shielded from common malware and unauthorized access. It is particularly well-suited for businesses that are transitioning away from legacy third-party antivirus solutions and want a security tool that is natively integrated into the Windows operating system. While it offers basic detection capabilities, its primary focus is on prevention, making it a cost-effective choice for organizations with a lower risk profile or those just beginning their journey toward a modern security architecture.
For organizations that operate in high-stakes environments, the gold standard is found in Plan 2, which expands the defensive capabilities into the realm of advanced forensics and automated intelligence. This tier encompasses every feature found in Plan 1 but adds the critical components necessary for a mature Security Operations Center, such as advanced threat hunting using the Kusto Query Language. With these tools, experienced analysts can proactively search through historical telemetry to identify subtle indicators of compromise that may not have triggered a standard alert. Furthermore, Plan 2 provides deep integration with the broader Microsoft 365 Defender XDR suite, allowing for cross-domain correlations that link endpoint events with identity and email threats. This level of sophistication is indispensable for large enterprises and entities in regulated industries like healthcare or finance, where the potential cost of downtime or data loss far outweighs the investment in a premium licensing tier.
Solutions for Small and Medium-Sized Businesses
The democratization of high-end security tools has reached a new milestone with the introduction of specialized offerings tailored specifically for the mid-market segment. Microsoft Defender for Business represents a strategic pivot designed to provide the small and medium-sized business market with nearly all the investigative power of the enterprise-grade Plan 2, but without the administrative overhead typically associated with such tools. It provides sophisticated endpoint detection and response and vulnerability management in a streamlined interface that is designed to be secure by default. This approach acknowledges that a company with only 200 employees still faces the same caliber of threats as a Fortune 500 corporation but likely lacks a dedicated, around-the-clock security team to manage complex configurations. By simplifying the deployment and monitoring process, the platform allows smaller entities to maintain an elite defensive posture that would have been financially and technically out of reach only a few years ago.
Another highly effective pathway for smaller organizations involves adopting a comprehensive productivity and security bundle rather than purchasing individual licenses. Microsoft 365 Business Premium has emerged as a preferred solution because it includes Defender for Business alongside essential productivity tools and identity management features. This reflects a broader industry trend toward vendor consolidation, where businesses seek to reduce the complexity of their technology stack by sourcing their security, office applications, and cloud identity from a single, integrated provider. For a resource-constrained IT department, the value proposition of this bundle is significant; it secures the device itself, the user’s identity via advanced multi-factor authentication, and the data stored within cloud applications simultaneously. This holistic approach ensures that there are no gaps between disparate security products, creating a unified defensive shield that is much easier to manage and audit over the long term.
Critical Feature Analysis and Visibility
In the current threat landscape, visibility is the most valuable currency a security professional can possess during an active breach. Without the advanced response and telemetry capabilities found in Plan 2 or the dedicated Business tier, an organization is essentially operating in the dark once an attacker manages to bypass the initial defensive perimeter. Traditional security tools often stop providing data the moment a file is blocked, but modern threats frequently involve fileless techniques or the abuse of legitimate system tools that do not trigger standard antivirus signatures. By utilizing a license that supports full endpoint detection and response, organizations gain the ability to track an attacker’s lateral movement and identify exactly which credentials may have been harvested. This level of insight is the difference between a minor cleanup operation and a multi-week forensic investigation that costs millions in lost productivity and legal fees.
Furthermore, the integration of vulnerability management directly into the security agent provides a massive operational advantage that traditional third-party scanners cannot match. By having a real-time view of which applications are unpatched and which system configurations are non-compliant, IT teams can move away from the “scan and patch” cycle toward a model of continuous risk reduction. This consolidated view allows for a more cohesive narrative of an organization’s risk, showing exactly which machines are most vulnerable to the specific exploits currently being used by active threat groups. For those operating in compliance-heavy sectors, these automated audit trails and reporting capabilities are not merely convenient features; they are essential requirements for meeting the legal standards of due care. The ability to demonstrate that a vulnerability was identified, prioritized, and remediated automatically provides a level of defensibility that is critical during regulatory audits or insurance renewals.
Strategic Selection and Optimization
The process of selecting a licensing strategy must be grounded in a realistic assessment of an organization’s operational goals and its current technical maturity. A growth-oriented mid-market company, for example, might find itself at a crossroads where its existing security tools are no longer sufficient to protect its expanding digital footprint. In this scenario, moving to Plan 2 becomes an attractive proposition as the company begins to build out its internal IT capabilities and requires more granular control over threat hunting and forensics. Conversely, a smaller firm that is focused purely on operational stability might find that Plan 1 serves as an excellent temporary stepping stone while they modernize their infrastructure. For large-scale enterprises, however, there is rarely a substitute for the advanced features of Plan 2, particularly when they must support a diverse array of platforms including macOS, various Linux distributions, and mobile operating systems, all while maintaining a centralized management plane.
Simply purchasing the most expensive license is rarely enough to guarantee security; the real value is extracted through a rigorous and ongoing optimization path. Many organizations fall into the trap of “shelfware,” where they pay for advanced features that are never properly configured or monitored, leading to a false sense of security. To avoid this, security policies such as attack surface reduction rules must be carefully tuned to the specific needs of the business environment to ensure they do not inadvertently block legitimate workflows while still providing a robust defense. Furthermore, Defender for Endpoint should never exist in a functional silo. It provides the greatest benefit when it feeds its rich telemetry into a broader security information and event management system, such as Microsoft Sentinel. This integration allows the organization to view the entire attack chain across its cloud resources, identities, and endpoints, turning fragmented data points into a clear, actionable intelligence picture that can stop an attack in its tracks.
Human Enablement and Continuous Review
Technology, regardless of its sophistication, is ultimately only as effective as the people who are tasked with its daily operation. Training IT staff to correctly interpret the alerts generated by the platform and to conduct basic forensic investigations is an essential step in ensuring the license provides its full intended value. A security team that understands how to use the automated investigation tools can resolve incidents in minutes that might otherwise take hours of manual effort, effectively acting as a force multiplier for the entire department. This human-centric approach to security ensures that when a critical alert does arrive, the response is swift, coordinated, and accurate. As the threat landscape continues to shift, investing in the skills of the personnel who manage these tools is just as important as the financial investment in the licenses themselves, creating a culture of security awareness that permeates the entire organization.
The final consideration for any licensing strategy must be the implementation of a continuous review process to ensure the organization’s defensive posture remains resilient against emerging threats. Security is a dynamic field, and a configuration that was effective last year may be insufficient today as attackers develop new methods to bypass standard controls. Regularly auditing license usage helps identify if the organization is missing out on critical new protections or if certain advanced features have been disabled. This proactive stance allows a business to scale its complexity alongside its growth, moving from basic prevention toward a model of autonomous, proactive defense. By balancing the cost of the subscription against the potentially catastrophic financial and reputational impact of a data breach, decision-makers can build a security foundation that is prepared for whatever challenges the digital landscape presents. The transition to integrated, intelligent security suites reflects a strategic commitment to long-term resilience, ensuring that the organization remains protected, compliant, and ready to face the future.