Data Security
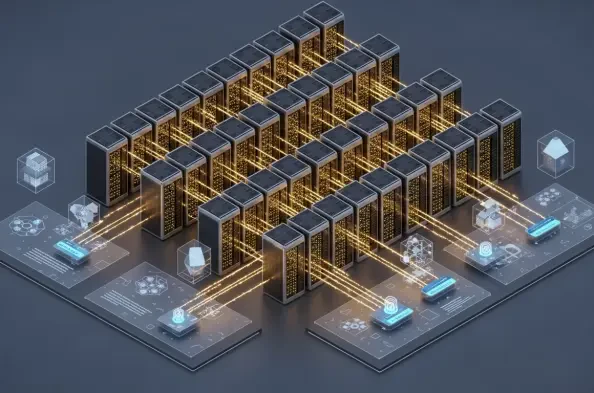
The rapid transition from simple text-based chatbots to autonomous entities capable of executing complex business logic has fundamentally altered the enterprise security landscape. While the Vertex AI platform provides a powerful suite of tools for building these agents, the underlying architecture introduces sophisticated risks that traditional
Corporate boardrooms across the United States are currently recalibrating their financial compasses to navigate a massive wave of capital toward sophisticated autonomous systems. Average corporate spending has hit $207 million as organizations pivot toward AI agents as the new core of enterprise strategy. This transition from simple chatbots to
Large enterprises are discovering that pouring billions into generative artificial intelligence without a robust cloud foundation is like trying to race a high-performance sports car through a dense, unpaved swamp. While the global appetite for automated decision-making and predictive analytics has reached a fever pitch, the underlying digital
The rapid arrival of functional quantum processors has shifted the cybersecurity conversation from a theoretical "what if" to a pressing "when," specifically regarding the looming threat of the "Harvest Now, Decrypt Later" strategy. This tactic involves adversaries intercepting and storing encrypted data today with the intention of cracking it
The relentless influx of security alerts in modern corporate environments often forces front-line analysts into a state of reactive fatigue where critical threats might slip through the cracks due to systemic inefficiencies. Rather than a lack of specialized training or individual talent, the primary bottleneck in contemporary Security Operations