The quiet residential street appears perfectly secure until a silent signal intercepted from the air allows a late-model SUV to pull out of a driveway without a single window being broken or a physical key being turned. This modern phenomenon, known as a relay attack, has transformed the traditional car thief into a high-tech hijacker who never needs to touch the vehicle to steal it. As the physical and digital worlds bleed into one another, the heavy brass keys that once defined our sense of safety are failing to protect the sophisticated computers we now call cars and homes. The vulnerability is no longer just a digital nuisance; it has become a tangible threat to our most valuable physical assets.
This shift represents a fundamental breakdown in the “single-factor” security model that has dominated human civilization for centuries. Whether it is a password for a thermostat or a signal from a key fob, relying on a single piece of evidence to grant access is becoming an invitation for exploitation. The integration of two-factor authentication (2FA) into the physical realm is no longer a luxury for the tech-savvy, but a necessary evolution in how society defends its property and personal safety. As every object becomes a node on the internet, the barrier for entry must move beyond a simple “something you have” to a more complex, multi-layered identity verification process.
The End of the Spare Key Era
The familiar jingle of metal keys in a pocket is rapidly becoming a relic of the past, yet the digital replacements we’ve embraced are proving surprisingly fragile. While a physical lock could be picked with a tension wrench, modern vehicles and smart homes are being “picked” by invisible code from across the street. This transition has happened so quickly that many consumers are unaware that their digital key is often less secure than the physical one it replaced. A single point of failure—be it a weak password or a clonable signal—now governs the security of our private sanctuaries.
As our most valuable physical assets join the Internet of Things, the stakes of a breach have shifted from stolen data to stolen property and compromised privacy. The convenience of keyless entry and remote access has created a massive security vacuum that traditional hardware cannot fill. We are living in an era where the hardware is smart, but the authentication methods are often stuck in the previous decade, leaving a wide-open door for anyone with a basic understanding of signal interception.
Why Tangible Assets Need Digital Bodyguards
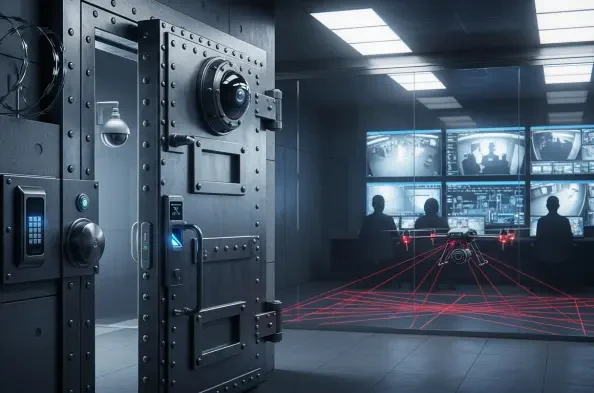
The convergence of the digital and physical realms has created a massive security vacuum that traditional locks cannot fill. Every connected device, from smart thermostats to industrial infusion pumps, represents a potential entry point for hackers looking to cross the threshold into the physical world. If a hacker can access a smart home network, they are not just looking at files; they are potentially controlling the locks, the cameras, and the climate systems that keep a family safe.
Furthermore, the failure of single-factor security is now a documented reality rather than a theoretical risk. Passwords can be phished and physical fobs can be cloned with inexpensive hardware available online, making “something you have” or “something you know” insufficient on its own. Unlike a stolen email password, a breach in physical security can result in the loss of high-value property or, in the case of medical devices, direct threats to human life. This escalation of consequences demands a bodyguard that lives in the digital layer but protects the physical one.
Expanding the Perimeter: From Screens to Real-World Hardware
Two-factor authentication is migrating from office logins to the objects we touch and use every day, creating a new standard for physical access. Organized crime rings now use relay attacks to clone key signals, but 2FA models like “pin-to-drive” or mobile app verification provide a secondary barrier that a cloned key cannot bypass. By requiring a second form of ID—perhaps a biometric scan on a smartphone or a unique code—the vehicle remains immobilized even if the primary digital key is successfully spoofed.
This shift in identity assurance is also critical in the healthcare sector, where connecting medical infrastructure to networks requires multi-factor authentication for clinicians. This ensures that only authorized personnel can adjust life-saving equipment like dialysis machines or infusion pumps. Security experts now argue that trust must be established through independent channels, ensuring that the person starting a car or accessing a medical record is verified by two separate pieces of evidence that do not share the same vulnerability.
Expert Perspectives on the Authentication Evolution
Industry leaders emphasize that the quality of security factors is just as critical as the presence of a second layer. Cybersecurity experts like Shane Barney note that physical world breaches have “real-life safety consequences,” moving the conversation from data protection to public safety. The consensus is that the industry must move away from easily intercepted methods like SMS-based codes toward hardware-based tokens and encrypted proximity sensors. The focus is no longer just on blocking access, but on verifying intent through multiple, reliable streams of data.
However, the battle against friction remains a primary concern for developers like Dr. Bastian Holderbaum, who argues that if a security measure makes unlocking a car door too difficult, consumers will simply find ways to bypass it. The goal is to move toward Ultra-Wideband (UWB) technology, which can measure the exact distance between a key and a lock to prevent long-distance relay attacks without requiring the user to tap additional buttons. This “frictionless” approach aims to provide military-grade security that feels as seamless as a traditional door handle.
Implementing Robust Physical 2FA Strategies
Securing the physical world requires a strategic balance between high-level encryption and user experience. Organizations and manufacturers must adopt multi-channel verification, ensuring that the secondary factor travels through a completely different communication path than the primary one. For example, a car might communicate via Bluetooth with a fob while a smartphone verifies the user’s identity via a secure cellular cloud connection. This separation ensures that an attacker would need to compromise two entirely different technologies simultaneously.
To stay ahead of the curve, it is essential to prioritize proximity-based technology and address the regulatory gap by adopting international safety standards from organizations like SAE and ISO. Implementing “hidden” secondary factors, such as behavioral biometrics or location-based geofencing, can maintain high security without interrupting the user’s workflow. As we moved toward a more interconnected existence, the focus transitioned to building systems that recognized not just a token, but the specific, verified presence of a human being. The ultimate strategy became one of layered resilience, where the convenience of the digital age finally matched the security of the physical one.