Cloud Security
A silent intrusion into a centralized database during the final months of 2025 accomplished something far more dangerous than simply draining bank accounts; it effectively transformed the private residences of thousands of French citizens into verified targets for organized armed robbery. The breach of the French Shooting Federation, known as
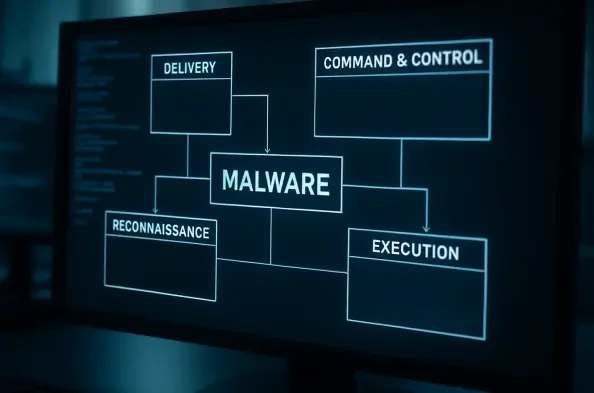
The silent infiltration of cloud-native infrastructure has entered a new phase of maturity where the distinction between professional security tools and malicious implants has effectively dissolved. Within this volatile landscape, the VoidLink malware framework has surfaced as a sophisticated, modular toolkit specifically engineered for
The Dawn of a New Era in Enterprise Financial Management The sheer velocity of artificial intelligence deployment has forced a radical restructuring of how the modern enterprise views every single dollar allocated toward its technological infrastructure. Once a niche discipline focused solely on monitoring cloud consumption, FinOps (Financial
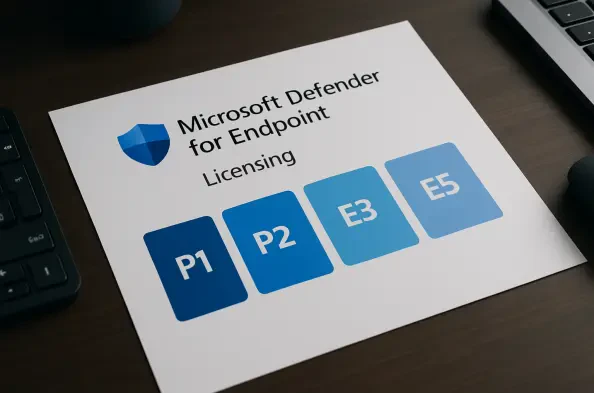
Modern cybersecurity professionals no longer view endpoint protection as a secondary defensive layer but rather as the primary battleground where the integrity of an entire corporate network is decided. Microsoft Defender for Endpoint represents a fundamental shift in how organizations approach this challenge, moving away from the antiquated model
The rapid ascent of autonomous AI agents has fundamentally altered the security landscape, introducing a new "Lethal Trifecta" of automation, entrenched system access, and untrusted inputs. As organizations and individual users flock to platforms like OpenClaw to streamline their digital workflows, they often inadvertently grant these agents the