Emerging Data Security Technologies
The rapid acceleration of quantum computing capabilities has turned what was once a theoretical academic concern into a pressing cryptographic emergency for global digital infrastructure. As of 2026, the transition from classical encryption methods like RSA and ECC toward quantum-resistant standards is no longer a luxury but a fundamental
The velocity at which generative artificial intelligence has permeated the modern corporate landscape is truly unprecedented, outstripping the adoption rates of the internet and smartphones by a significant margin. Current industry data suggests that daily enterprise usage has surged by nearly sixty percent over the last year, while weekly
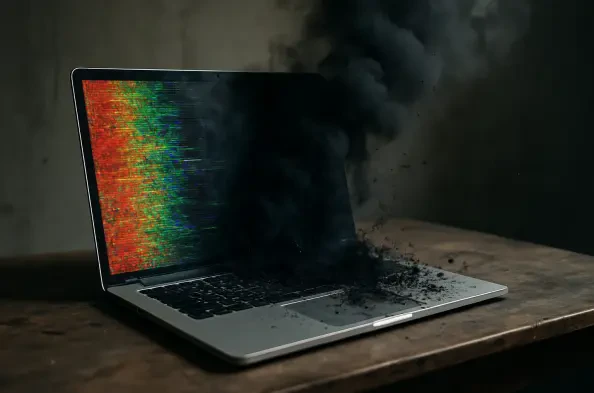
The landscape of digital threats has undergone a fundamental transformation, moving from the era of simple script-based viruses to a modern age dominated by AI-driven ransomware and highly targeted zero-day exploits. Navigating this environment requires more than just a passing familiarity with computer settings; it demands a comprehensive
The global digital infrastructure is currently grappling with a recursive paradox where the very systems built to process human knowledge are now starving for lack of authentic human interaction. As artificial intelligence continues to permeate every facet of professional and private life, the internet is becoming a mirror reflecting its own past
The massive surge in corporate artificial intelligence adoption has created a paradoxical landscape where technological velocity far outpaces institutional readiness. While nearly every global organization has initiated some form of automated pilot program, a staggering 71% of these enterprises are operating without a finalized strategic roadmap.