Secure Data Transfer
The strategic partnership between DXC Technology and Amazon Web Services (AWS) represents a significant advancement in enterprise AI adoption. This review will explore DXC's "customer-zero" strategy for deploying the Amazon Quick AI agent builder, its key features, early performance metrics, and the impact it has on the IT consulting landscape.
The Great Re-Evaluation: Why Everyone Is Talking About Virtualization Again The enterprise IT world is buzzing with a conversation that many thought was settled years ago: virtualization strategy. Catalyzed by Broadcom's acquisition of VMware and its sweeping changes to licensing models, a wave of strategic re-evaluation is coursing through
Microsoft's latest security advancements, introduced under its Secure Future Initiative, signal a fundamental reevaluation of operating system protection by shifting from a reactive posture to a proactive, default-on defense. This review explores the evolution of Windows security, its key new features, performance implications, and the impact it
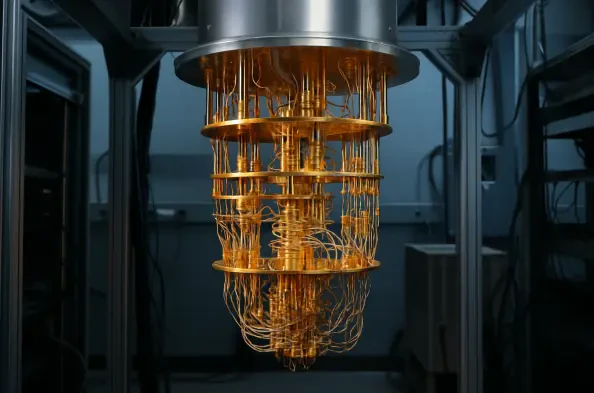
In the silent, high-stakes arms race of the digital age, a new and formidable threat is emerging on the horizon, one capable of shattering the very foundations of modern cryptography. The advent of quantum computing promises to unlock unprecedented computational power, but it also carries the potential to render secure communications and digital
The polished privacy dashboards and reassuring corporate statements from Big Tech often obscure a stark reality where the most robust security protections remain just out of reach for the average user, locked behind optional settings and unfulfilled promises. This growing divide between the marketing of privacy and the mechanics of its