Grace Wainaina
Privacy Compliance ExpertThe simple convenience of scanning a square of black and white pixels to pay for a parking spot or view a digital menu has morphed into a sophisticated vector for cybercriminals seeking to harvest sensitive user credentials without the target ever realizing a breach has occurred. While these Quick Response codes were originally designed for
Managing an internal data estate that encompasses more than one hundred thousand distinct tables requires a fundamental shift in how modern technology enterprises approach the concepts of security and accessibility. As Databricks expanded its operations, it encountered the formidable challenge of overseeing a massive volume of engineering
The transition from static generative chat interfaces to autonomous digital agents represents one of the most significant architectural shifts in the history of enterprise computing. These sophisticated systems are no longer content with merely summarizing documents or drafting emails; they are increasingly tasked with navigating complex software
The digital perimeter of modern retail is no longer defined by a single firewall but by an intricate web of third-party integrations that often outlive their operational usefulness. The recent security incident involving Zara, the flagship brand of the Inditex group, serves as a stark reminder that data remains vulnerable long after a formal
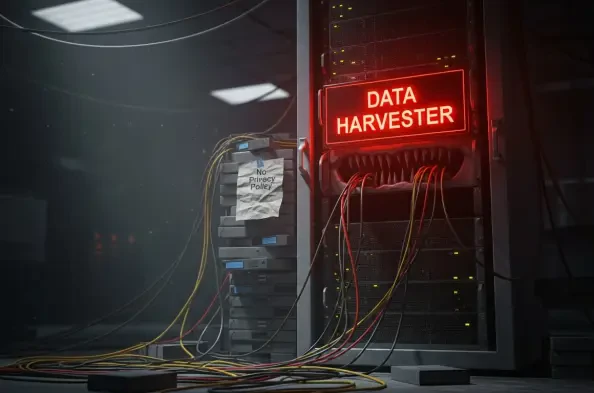
The rapid digital transformation of government services in Nigeria has created a significant gap between technological adoption and the fundamental protection of individual digital rights. In Katsina State, a troubling pattern has emerged where sensitive personal information is harvested through official channels without the basic transparency of
The promise of a friction-less financial reporting landscape in the United States remains a distant aspiration despite the clear legislative mandates established several years ago. When the Financial Data Transparency Act was integrated into the broader defense authorization framework, it was heralded as the definitive solution to the fragmented