Data Security
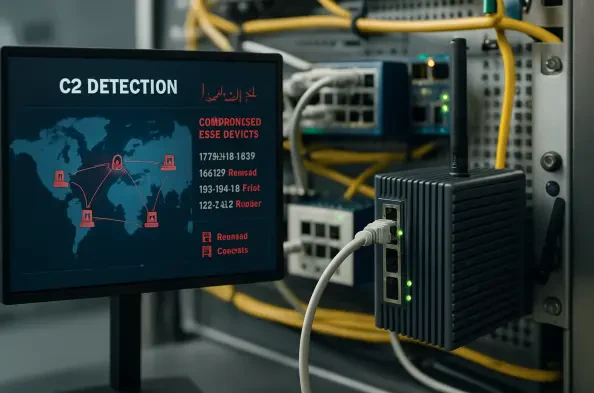
The persistent vulnerability of perimeter hardware has long served as a quiet sanctuary for sophisticated cyber threat actors who exploit the inherent lack of visibility within these critical systems. While traditional endpoints like workstations and servers benefit from robust security stacks including endpoint detection and response tools, edge
The Great Virtualization Migration: An Industry at a Crossroads The massive upheaval currently rattling the enterprise virtualization market is driven by a startling revelation that half of all existing customers are looking to move away from their primary vendor. Following the high-profile acquisition of VMware by Broadcom, an independent survey
Vernon Yai is a distinguished authority in data protection and privacy governance, renowned for his strategic approach to risk management and the implementation of advanced detection techniques. With a career dedicated to safeguarding sensitive information, he has become a leading voice for organizations navigating the increasingly complex
The persistent vulnerability of data during active processing has long been the Achilles' heel of digital security, forcing organizations to choose between the scalability of the cloud and the sanctity of their most sensitive information. Niobium, a specialized hardware acceleration firm headquartered in Dayton, Ohio, is challenging this
The dramatic reduction in the technical and financial barriers to entry has fundamentally redefined the cryptocurrency landscape as of early 2026. For much of the past decade, the act of securing a blockchain network through mining was a specialized endeavor that required a prohibitive combination of expensive hardware, deep technical mastery, and
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114